TESS TMS
Threat Management System for proactive cyber threat response
TESS TMS (Threat Management System) is an intelligent network security management platform that monitors incoming traffic in large-scale network environments in real time and detects and blocks external attacks and attempts at internal data leakage through an advanced intrusion detection engine. With powerful analytics capabilities, it eliminates security blind spots and ensures operational reliability through features such as real-time leakage rate monitoring, delivering optimal network security availability.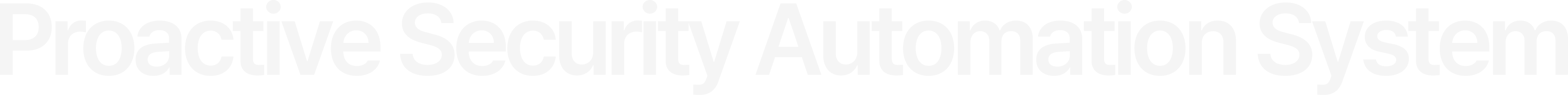
TESS TMS Framework
Based on network traffic and detection events collected from sensors,it analyzes threat indicators to enable comprehensive identification of attack flow.

Major Features
-

Attack Detection
Signature-based advanced detection of known threats such as DoS and malware
-

Malicious Traffic Data Collection & Analysis
In-depth analysis of malicious traffic and user-centric visualization dashboards
-

Policy Management
Configuration and management of detection policies for network and security threats
-

Detection Intelligence Integration
Sharing detection intelligence with external ESM and SIEM systems, with support for policy integration with firewalls (FW) and IPS
-

File Collection & Malware Detection
Detection and collection of file transfers within traffic, and advanced malware analysis based on YARA
-

IP Reputation Matching
Intelligent threat analysis engine utilizing global IP reputation data by attacker IP
-

Application Detection
Automatic analysis and detection of L7-level applications without requiring separate policies
-

Asset Discovery & Learning
Identification of internal asset information discovered during analysis to support continuous asset visibility and management
Distinct Features
-
Threat Detection
& Analysis - Sandbox PCRE/YARA
- Advanced malware analysis through sandbox integration and YARA engine. Supports analysis of Suricata, Snort, PCRE, YARA, and applications.
-
Advanced Malware
Response -
Sandbox-Integrated Analysis
Multi-Engine Threat
Detection - In-depth analysis of advanced intelligent malware using sandbox integration and YARA engines. Comprehensive threat detection through integrated operation of Suricata, Snort, PCRE, and YARA engines.
-
Performance
& Reliability -
Minimized Packet Loss
Real-Time Loss Rate
Monitoring Optimized Data Analysis -
Minimizes packet loss even in high-volume traffic environments through high-performance dedicated hardware
and optimized analysis engines. Provides real-time metrics on processing status and loss rates to verify the reliability of data collection. Improves analysis efficiency through event refinement and lightweight processing,
minimizing the transmission load to upper-level systems.
- Visibility
- Intuitive UI/UX Reduced Analysis Time
- User-friendly management environment through data visualization and diverse statistical insights. Supports rapid decision-making with an integrated UI centered on key events.
-
Precise Analysis
& Visibility -
XFF-based Real
IP Identification GZIP Compressed
Traffic Analysis Encrypted Threat
Analysis Support VXLAN Tunneling
Analysis - Identifies and manages the actual client IP by analyzing X-Forwarded-For (XFF) headers even in proxy/L4 environments. Detects threats within compressed web traffic without gaps using a built-in GZIP decompression engine. Performs deep packet inspection (DPI) on decrypted traffic when integrated with external decryption devices. Provides in-depth analysis of VXLAN virtual network traffic to ensure visibility in virtualized environments.
- Forensics
-
Log with Stream
Detailed Analysis
Data Provision - Supports detailed tracking of attack context with optional storage of additional packets before and after event matching. Improves analysis accuracy by providing real-time RAW data and stream information related to threat events.
-
Infrastructure
Flexibility - SSL/TLS Native Analysis Support for Universal Virtual Environments Multi-Cloud Compatibility
- Detects threats in encrypted traffic based on metadata through native SSL/TLS analysis. Fully supports KVM/QEMU and image installations (ISO, VMDK, etc.), as well as standalone OS environments. Provides optimized security features and services for various domestic and global cloud infrastructure environments.





