Security Solutions
TESS NDR
An Intelligent Network Detection and Response System for Intuitive Threat Analysis and Response
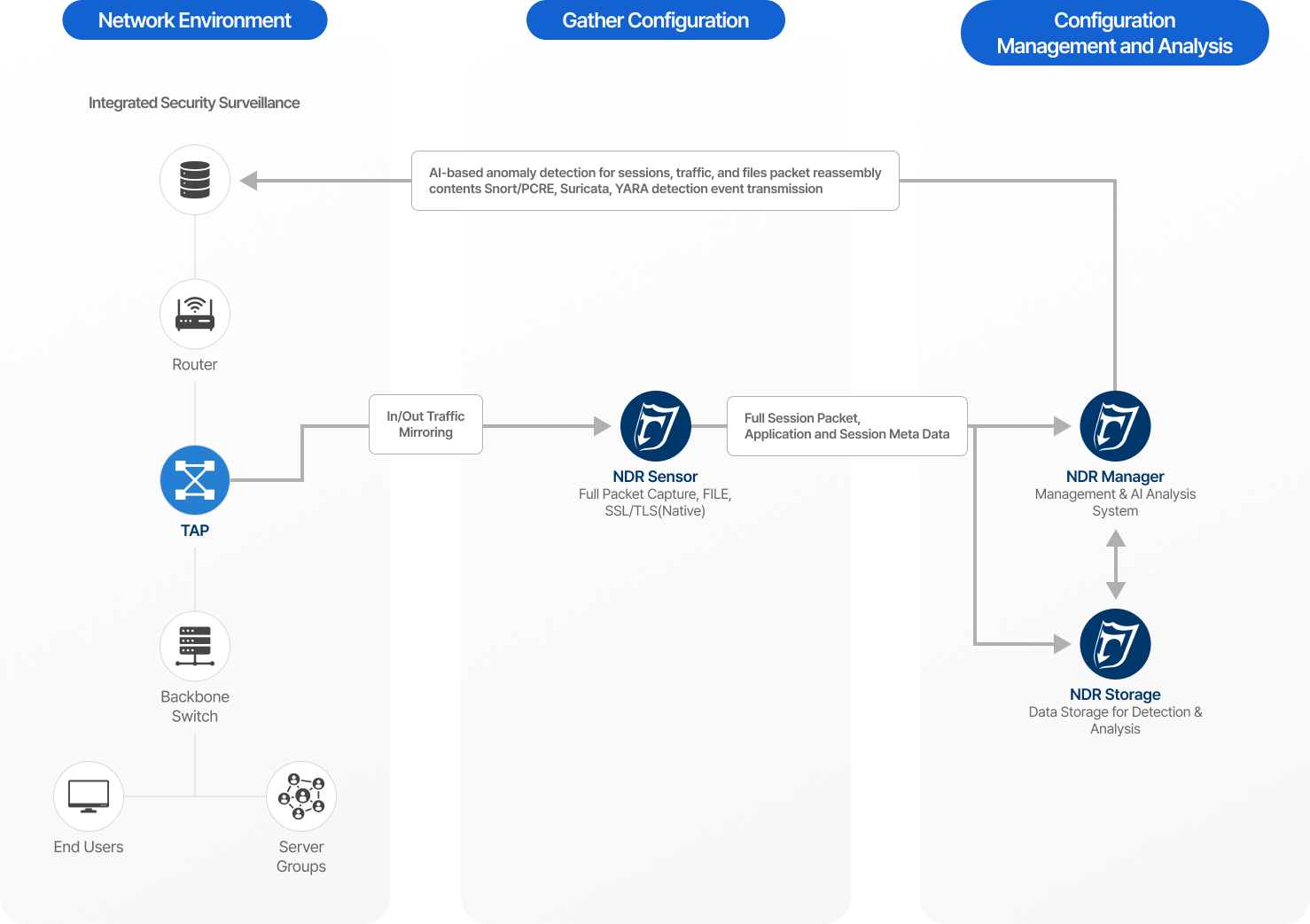
TESS NDR (Network Detection and Response) is a next-generation platform that collects and analyzes network-wide traffic in real time, identifying advanced threats and internal intrusion activities that are difficult for conventional security solutions to detect. Beyond simple event log analysis, it combines full packet capture with AI-based behavioral analytics to visualize the entire attack lifecycle and provide a proactive defense framework against sophisticated threats.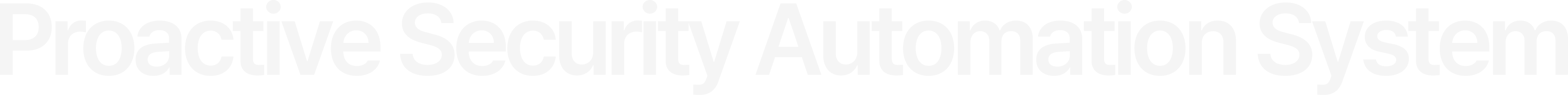
TESS NDR Framework
For full session packets collected by NDR sensors and network/file detection events,threat indicators are analyzed using AI for comprehensive identification of attack flow.
Major Features
- Traffic Management
-
Full Packet Retrieval
& Extraction High-Speed Metadata
Analysis -
Enables detailed queries of stored raw packet data (based on Lustre distributed storage)
by time/conditions and supports file extraction. Utilizes GPU acceleration to rapidly search and analyze session/app metadata extracted from large-scale traffic.
- Threat Analysis
-
Behavior-Based Anomaly
Detection Alerts Precise Malicious File
Inspection Real-Time Global
Reputation Matching - Generates real-time threat scoring and alerts for abnormal traffic patterns detected using ML models (e.g., Random Forest). Analyzes features of files extracted from traffic and compares them with predictive models to determine maliciousness. Integrates with external CTI to compare IP/file reputation in real time for immediate threat identification.
- Tracking & Investigation
-
MITRE ATT&CK-Based
Tracking Incident Timeline
Reconstruction - Maps detected attack behaviors to ATT&CK tactics and techniques to track the attack stage (e.g., intrusion, lateral movement). Arranges event flows chronologically before and after incidents to help administrators understand the full context of a breach.
- Asset Management
-
Asset-Based Threat
Correlation Analysis Host Activity
History Management - Identifies relationships between attackers and affected assets based on assets/IPs and analyzes threat propagation paths. Manages all threat events and communication history for specific hosts, serving as key evidence for incident investigations.
- Operations & Reporting
-
Threat Flow Visualization
Automated Customized
Analysis Reports - Visualizes detection data in flow charts for intuitive monitoring of complex network threat progression. Generates security analysis reports based on detected threats and collected traffic statistics for specified periods.
Distinct Features
- High-Speed Analysis
- Lossless Full Data Collection
- Combines Full Packet Capture modules with GPU acceleration to ensure 100% real-time packet collection without loss, even in ultra-high bandwidth environments (10G+), enabling reliable forensic analysis.
- Intelligent Detection
- Proactive Response to Unknown and Evasive Threats
- Uses ML models (e.g., Random Forest) to identify unknown, signature-less attacks and evasive traffic, enabling proactive defense against advanced persistent threats (APTs).
- Precise Identification
- Minimized False Positives through Multi-Dimensional Analysis
- Maximizes detection accuracy by applying feature engineering techniques that integrate packet data, file inputs, and signature information.
- Tactics Tracking
- Visualization of the Entire Attack Lifecycle
- Maps all detected events to MITRE ATT&CK techniques in real time, providing intuitive visibility into the full attack scenario from initial intrusion to the current stage.
- Operational Reliability
- Stable Big Data Processing Platform
- Utilizes a large-scale clustered Lustre distributed file system to manage massive data reliably Supports REST APIs for seamless integration with existing security infrastructure (e.g., SIEM, SOAR) and enables automated response workflows.



